Cyber security for plants
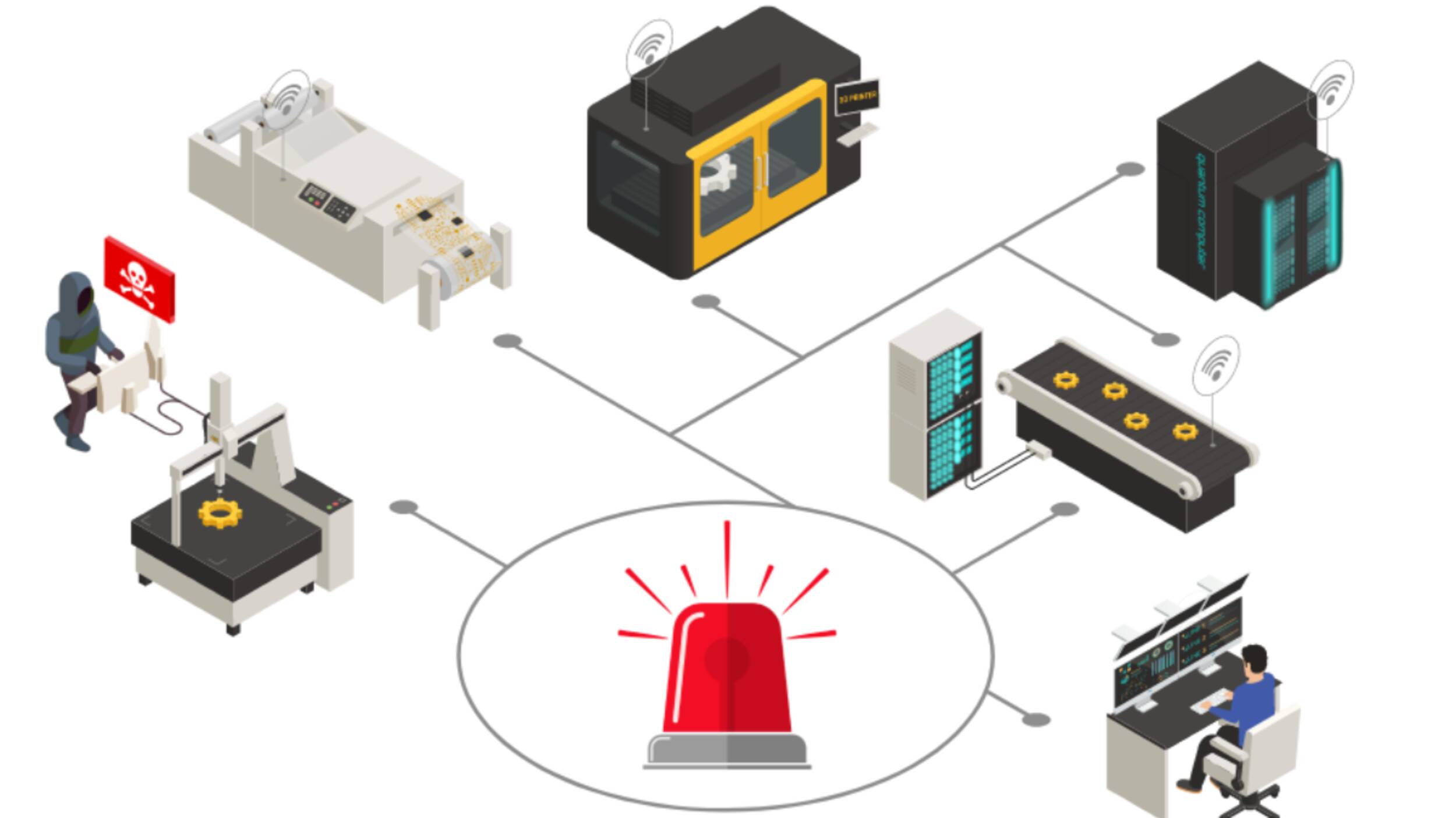
Many companies focus on IT when it comes to cyber security. This completely neglects systems for controlling plants where mechanical, electrotechnical and software components are interconnected and communicate via a data infrastructure such as the Internet!
In short, operational technology (OT) controls the assets and information technology (IT) controls the data. The OT security takes care of protecting the hardware and software that are used to monitor and control physical processes, facilities and infrastruc-
tures. The main focus is on the control systems such as PLCs, including SCADA as well as process control systems
which are used in industrial plants and physical machines.
Such plants are increasingly integrated into IT networks, resulting in new vulnerabilities that can stop or manipulate (critical) plant processes and force a company to shut down. Likewise, plants and plant networks become a gateway for cyber attacks with far-reaching consequences for a company. This makes it all the more important to have a practicable approach to threats that go hand in hand
with IT security.
OT-Security is crucial:
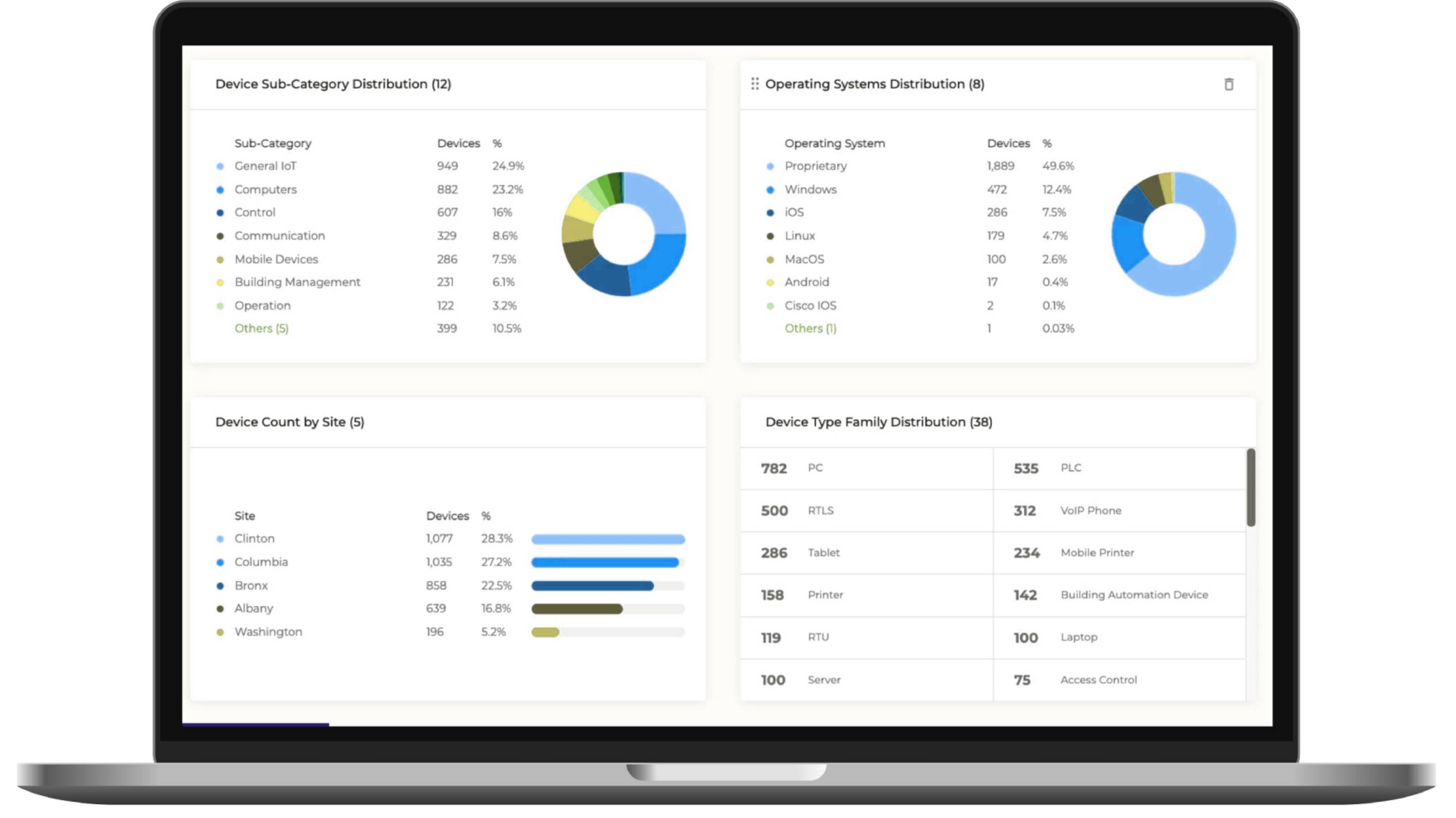
Full Transparency
Every asset and device in the OT network is detected, continuously analyzed and "taken care of" according to the exposed threats.
Maximum control
Employee and external access permissions to segmented facility networks with multifactor authentication.
Active network monitoring
Continuous behavioral analytics that provide accurate information about what is going on in the network (what, where, when, who, how).
Failures in plant
- Missing network segmentation of included assets
- Missing or neglected access controls to assets e.g. via remote access via VPN
- Missing active network monitoring
- Missing vulnerability assessment of each asset and control device (inventory)
Risks that result
- Increased vulnerability to cyberattacks
- Business and financial losses due to system interruptions
- Loss of sensitive data and intellectual property
- Danger to the safety of employees and the public due to malfunctioning OT systems
Service of Rey
- Inventory (asset discovery)
- Vulnerability management
- Risk management with recommendations for action
- Real-time network monitoring
- Incident response management
- Audit and compliance report
Want to know more?
Sandro Gloor will be happy to show you,
what benefits you can achieve in your company.
sandro.gloor@rey-technolog.com
+41 58 810 04 81